A feature of the apache webserver is that it allows to to create a SSH connection through a transparent proxy / firewall. This is a stealth technic so no one will see it even in a large company network. Only IPoAC is able to interference this.
If you have internet access to port 80 (http) or 443 (https) you can establish a SSH connection to one of that ports. Proxys want the users to surf the web. most of the proxyes will only let their users through the paths they know safe (or whatever filtering their administrators may have set). In the best scenario, the proxy will not allow one particular HTTP method called CONNECT. This method is the one used for SSL / TLS protocol. It establishes a tunneled connection between the client and a remote server, through the proxy server. Since it is used by SSL / TLS, some proxys will let the CONNECT method free to certain sites, and most probably only on port 443.
Apache plus mod_proxy module will let us set up an HTTP server listening on port 80, and at the very same time an HTTP proxy. The proxying part is done by mod_proxy. This module turns Apache into a fully functional HTTP forward-proxy and reverse-proxy. the exciting feature of mod_proxy is its ability to handle the CONNECT method. It will even handle it if the transparent proxy, at the boundaries of our enterprise network, does not allow the CONNECT method. This, because we will talk GET and POST with Apache, the CONNECT thing happens inside Apache, and outside of the control of the enterprise proxy. The end result: we can use the CONNECT method.
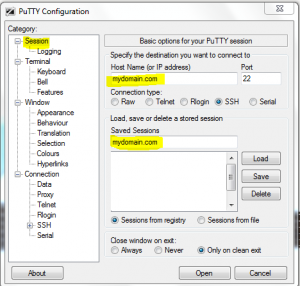
Client side
- SSH Client
- Proxyclient
server side
- apache webserver 2.x
This is an example virtual host configuration which I used for testing this implementation.
<VirtualHost *:80> ServerName proxy.mydomain.com ProxyRequests On AllowCONNECT 22 <Proxy *> Order deny,allow Deny from all </Proxy> <ProxyMatch (host1|host2)\.mydomain\.com> Order deny,allow Deny from all #Now we allow only our IP to access. Note that this IP must be the public IP address of the enterprise proxy: Allow from 222.22.22.100 </ProxyMatch> # This directive enables DNS lookups so that host names can be logged. The value Double refers to doing double reverse DNS lookup. #That is, after a reverse lookup is performed, a forward lookup is then performed on that result. At least one of the IP addresses in the forward lookup must match the original address. It is paranoid but is a good security measure HostnameLookups Double ErrorLog /var/log/apache2/proxy.error.log CustomLog /var/log/apache2/proxy.access.log common </VirtualHost>
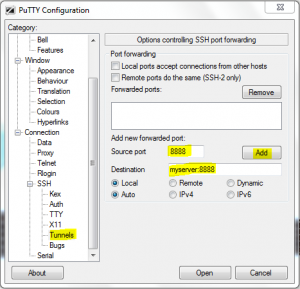
And now, the final step: configure our browser to use 127.0.0.1 on port 8080 as proxy. Finally we can login to our SSH server and try pointing our browser to any website we know blocked by the enterprise transparent proxy!
I know I left the part setting up apache and proxy, but this isn’t a tutorial for noobs ;-)
This is the BEST part of using Apache. You can set it up as normal web server, serving some webpage. This way whoever point to mydomain.com will see a normal and harmless website, and won’t be able to distiguish it from a non-proxying server.


Thanks for your post. I was looking at various means to do tunneling of SSH through transparent proxies run by ISPs.
Before I start building what you’ve suggested, let me understand the architecture.
Local PC -> Apache on local PC with mod_proxy -> to the outside world via ISP transparent proxy.
Is my understanding right?
Thanks.
This does work only if apache is behind that transparent proxy
Hi,
The interesting part which I liked about your article is the ability to talk GET/POST with apache so that CONNECT thing happens only on remote computer.
I have setup my home ssh server with apache mod proxy on port 80. I connect to outside world from work through a proxy. Currently I configured cygwin & proxytunnel at work to connect to my home apache/ssh server. The error I get is: “ISA Server is not configured to allow SSL requests from this port. Most Web browsers use port 443 for SSL requests”.
Is there a workaround for this, so that I keep my ssh server with apache at port 80?
How can I force my ssh client (cygwin). or any other client which i can FORCE to use the GET method and NOT the CONNECT method?
It is how your ip address can shift online